Tsundere Botnet Uses Blockchain to Target Windows Users

Kaspersky Lab researchers have discovered a new botnet named Tsundere that targets Windows devices using PowerShell scripts or MSI installers. The malware distributes itself by masquerading as installers for popular games including Valorant, CS2, and R6x.
Geographic Targeting
Tsundere attacks have been recorded primarily in Mexico and Chile. Technical analysis indicates the malware attempts to avoid infecting systems in CIS countries, though infections have also been observed in Russia and Kazakhstan.
Campaign Origins
Researchers linked Tsundere to incidents from October 2024, when threat actors created malicious Node.js packages and used npm to deliver payloads. At that time, 287 malicious packages were identified that employed typosquatting—their names resembled slightly altered versions of popular libraries like Puppeteer and Bignum.js.
Blockchain-Based Infrastructure
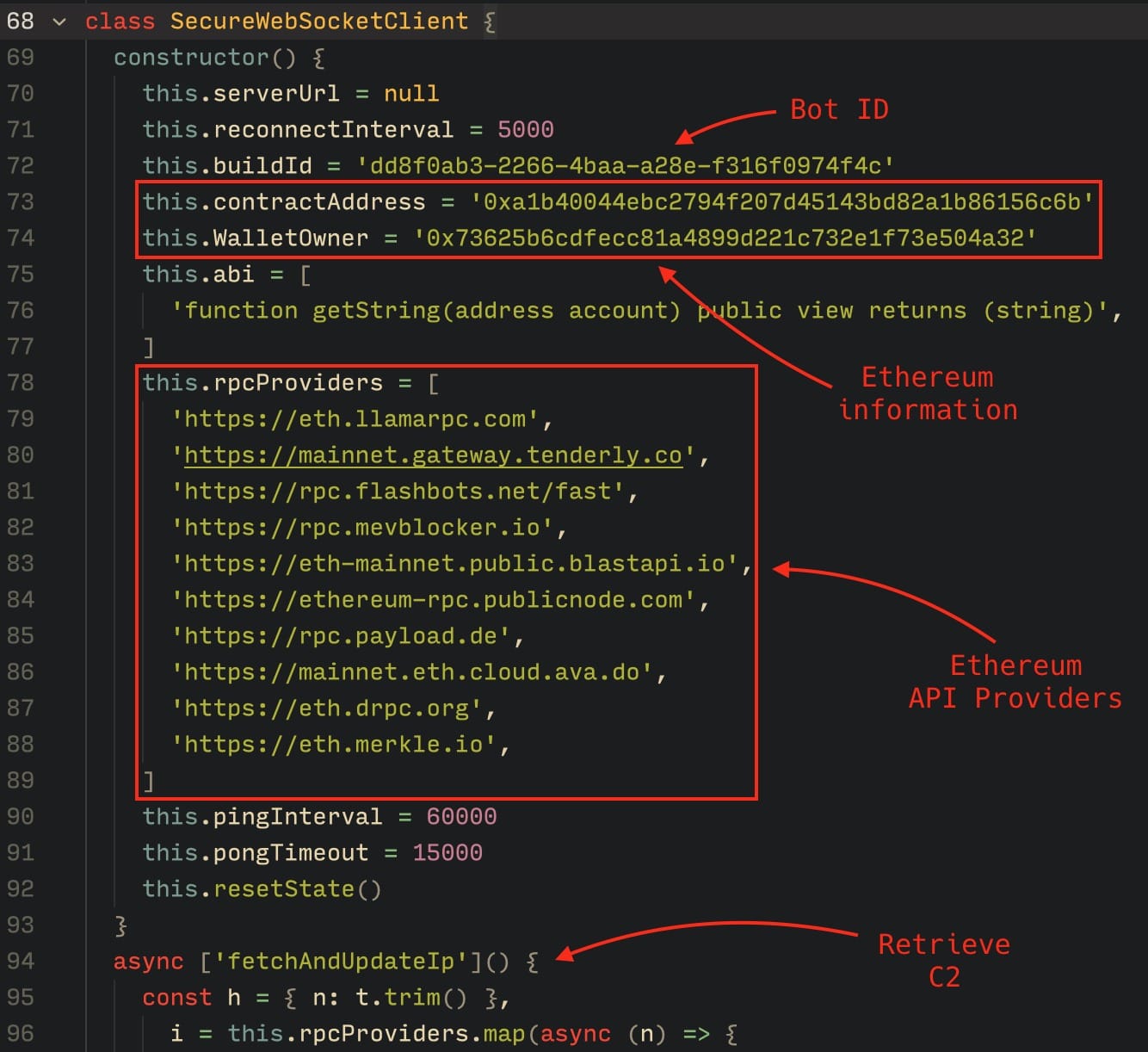
Tsundere uses Web3 smart contracts to host the addresses of its command-and-control (C2) servers, a tactic gaining popularity among threat actors due to increased infrastructure resilience.
The malware has two distribution formats that are generated automatically: MSI installers and PowerShell scripts. These implants install a bot on compromised devices that can continuously execute JavaScript code. Tsundere uses WebSocket as the primary protocol for communicating with command servers.
A notable feature of this malware is its use of the Ethereum blockchain to switch between command servers. This tactic significantly enhances the botnet infrastructure's resilience: even if one command server is blocked, bots automatically switch to backup addresses recorded on the blockchain.
Per the researchers, the botnet uses smart contracts to store encrypted configurations. To change the command server, malware operators make a 0 ETH transaction, writing the new WebSocket server address into the contract's state variable. The bot accesses public Ethereum RPC endpoints, analyzes transactions, and extracts the current C2 address.
Attribution Indicators
The Tsundere botnet developers are likely Russian-speaking, based on code elements and other indicators. The investigation revealed connections between Tsundere and 123 Stealer—a stealer distributed on hacking forums. Both threats share common infrastructure and are linked to a user named 'koneko', whose darknet profile identifies them as a "senior developer of node malware."
"The analysis of Tsundere showed how quickly threat actors adapt to modern conditions: apparently, they have already repeatedly tried to update their toolkit. After moving to Web3 mechanisms, the attackers' infrastructure became more flexible. We see that the implants continue to be distributed under the guise of game installers, and a connection to previously detected malicious activity is also traced. Therefore, the botnet is likely to continue expanding," commented Dmitry Galov, Head of Kaspersky GReAT in Russia.


