Shai-Hulud Worm Returns to npm, Compromises Over 25,000 Developers
The self-propagating Shai-Hulud malware has returned to npm, compromising over 25,000 developers in just three days. Hundreds of infected versions of popular packages—including Zapier, ENS Domains, PostHog, Postman, and AsyncAPI—were uploaded to npm to steal developer and CI/CD secrets.
Scale of the Attack
According to analysts from Wiz, as of November 24, 2025, over 25,000 repositories on GitHub had published secrets stolen from victims, with approximately 1,000 new repositories being added every 30 minutes.
Bleeping Computer reported about 27,600 results related to this attack on GitHub. Wiz researchers discovered approximately 350 unique npm accounts involved in the malicious campaign.
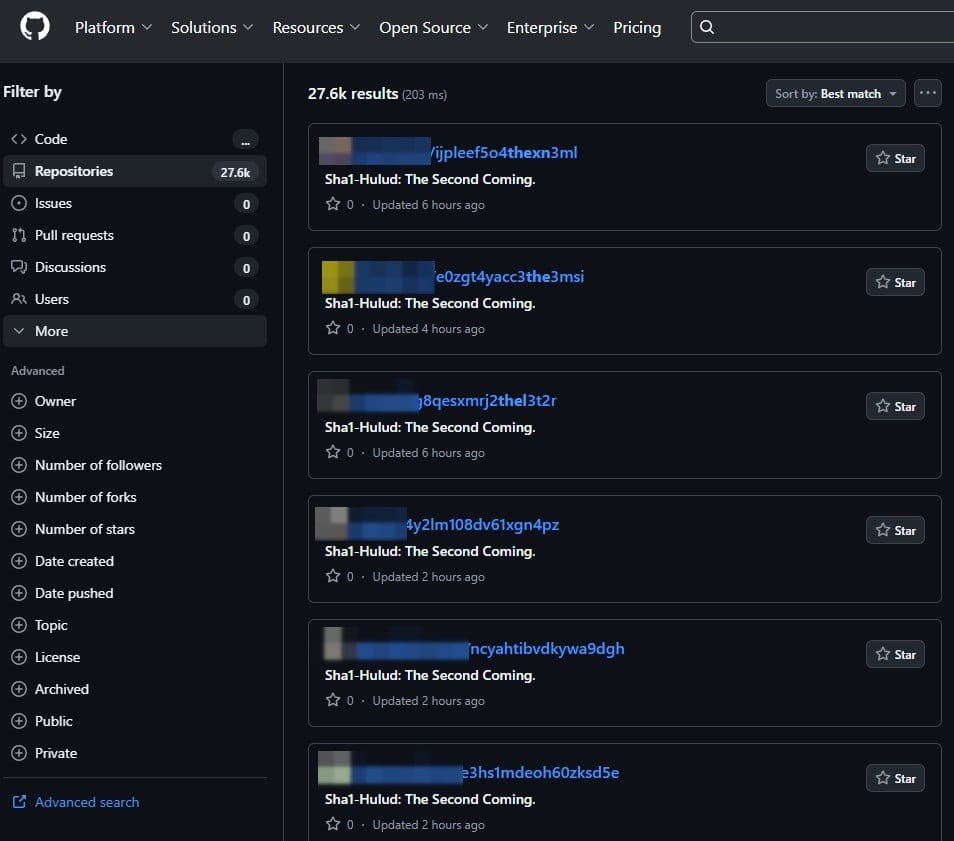
The GitHub repositories indicate compromised developers who used the trojanized npm packages and had GitHub credentials in their environment. Although GitHub representatives are actively removing repositories containing compromised data, the worm is spreading faster than the cleanup efforts.
Background: The Original Attack
The Shai-Hulud worm was first observed in mid-September 2025, compromising 187 packages in npm. The worm used the legitimate TruffleHog tool—a secret scanner intended for developers and security professionals—to find and steal developer secrets.
The worm created public copies of any private repositories belonging to compromised users to access hardcoded secrets and steal source code. All newly created repositories had the suffix "migration" added to their names.
A self-propagation mechanism was embedded into infected package versions, targeting other packages maintained by affected maintainers. The malware downloaded each of the maintainer's packages, modified its package.json, injected a bundle.js script, repackaged the archive, and published it again, thereby "ensuring the automatic trojanization of downstream packages," as researchers explained.
Shai-Hulud 2.0: Enhanced Capabilities
In the new version (Shai-Hulud 2.0), a key difference is the execution of malicious code at the pre-install stage, which significantly increases the risks.
Technical analysis conducted by Step Security shows the malware consists of two files: setup_bun.js (a dropper disguised as a Bun installer) and bun_environment.js (10 MB), which uses complex obfuscation techniques including a hex-encoded string with thousands of entries, a separate loop for anti-analysis, and an obfuscated function to extract each string in the code.
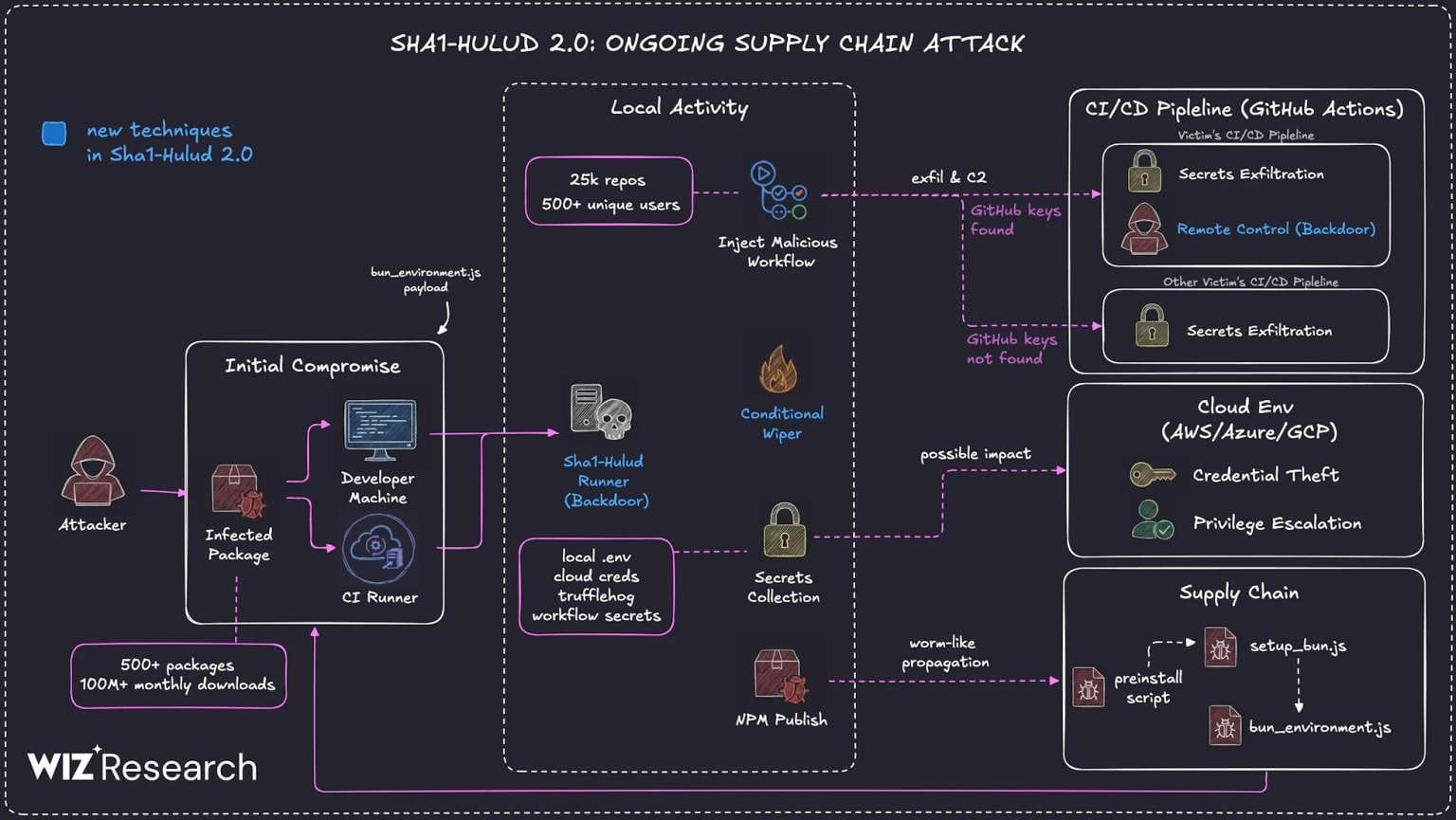
After infection, the malware executes five attack stages, including extracting secrets (GitHub and npm tokens, AWS, GCP, Azure credentials) and destructively overwriting the victim's entire home directory if four required conditions are not met: if the malware cannot authenticate to GitHub, create a repository, or find GitHub and npm tokens.
The stolen secrets are published to automatically generated GitHub repositories with the description "Sha1-Hulud: The Second Coming."
Affected Packages
According to researchers from Aikido Security, about 500 compromised packages have been identified, while Koi Security found over 800 malicious packages (counting all versions). Affected packages include:
Zapier - The official toolkit for integrations
ENS Domains - Tools and libraries for working with wallets, DApps, exchanges, and the ENS Manager app for handling .eth names, converting them to Ethereum addresses, linking IPFS content, verifying names, and interacting with official ENS smart contracts
AsyncAPI, PostHog, Postman - Popular tools with thousands of weekly downloads
Mitigation Steps
Researchers urge developers to take immediate action:
- Clear npm cache and revert to package versions published before November 21, 2025
- Immediately replace all CI/CD secrets and tokens
- Manually check repositories for new publications and suspicious commits mentioning "hulud"
- Disable postinstall scripts in continuous integration environments where possible
GitHub's Response
Following the recent Shai-Hulud and S1ngularity attacks, GitHub developers promised to enhance security measures, including requiring two-factor authentication for local publications, limiting the lifespan of Personal Access Tokens (PAT) to seven days, phasing out time-based one-time passwords (TOTP) in favor of FIDO-based authentication, and other improvements. However, these measures are being implemented gradually.


